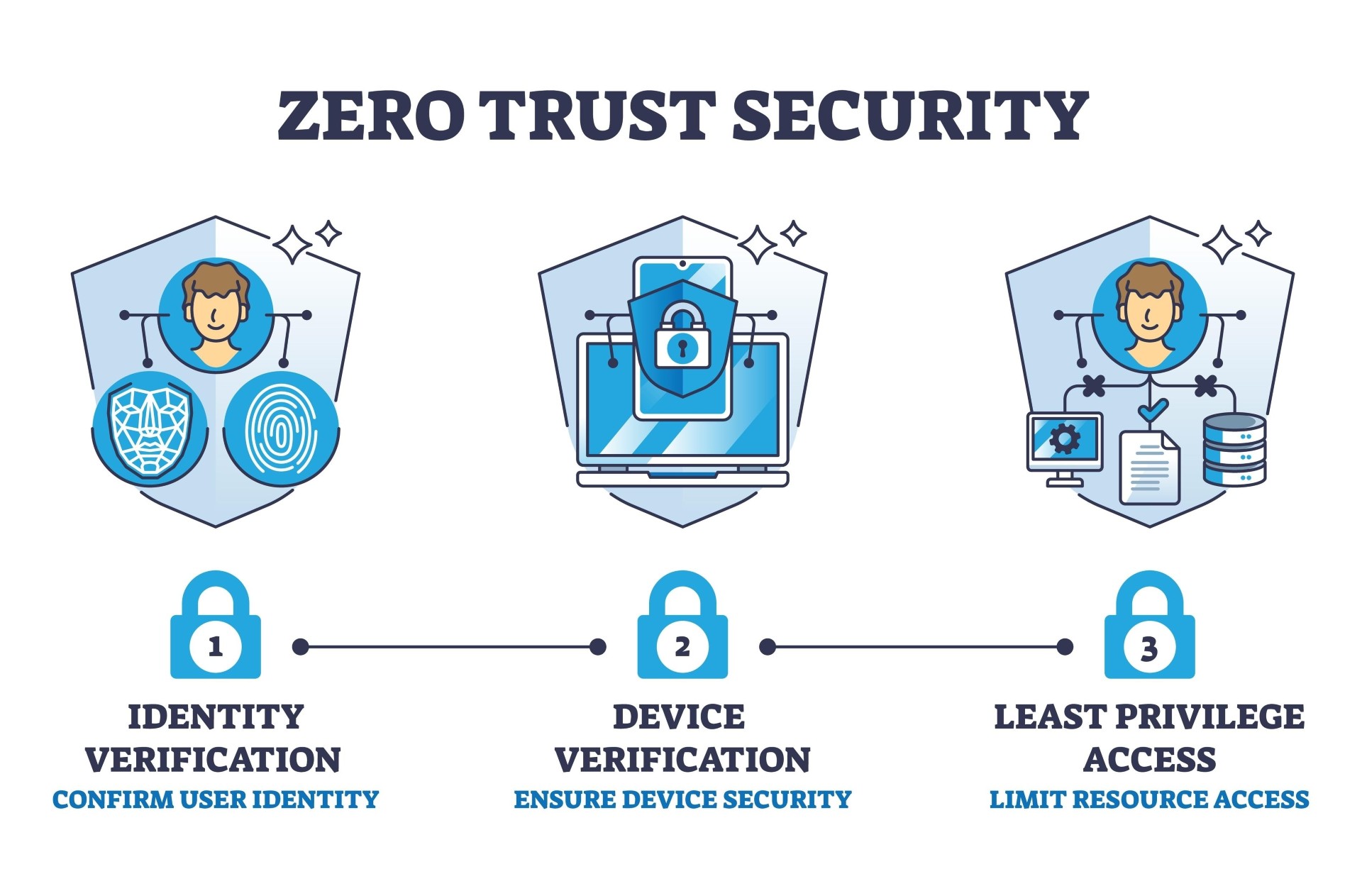
The traditional cybersecurity perimeter is obsolete. In an era defined by remote work, cloud adoption, and a proliferation of unmanaged devices, relying on network boundaries like firewalls and VPNs leaves organizations vulnerable. The modern standard for robust cybersecurity is Zero Trust Architecture—a model built on the principle of “never trust, always verify.”
The Challenge: Beyond the VPN
Historically, once a user authenticated through a Virtual Private Network (VPN), they were granted broad access to the corporate network. Today, this “castle-and-moat” approach is a massive liability.
- Over-Privileged Access: Compromised credentials can give attackers lateral movement across the entire network.
- The BYOD and Third-Party Dilemma: Securing access for contractors, partners, and employees using personal devices (BYOD) is a logistical nightmare with traditional agents.
- Poor User Experience: Legacy VPNs often suffer from latency, creating bottlenecks and frustrating the modern workforce.
Organizations need a solution that grants access based on identity and context, rather than network location. This is where Zero Trust Network Access (ZTNA) becomes essential.
Red Access: Redefining Zero Trust at the Browser Level
Implementing Zero Trust doesn’t have to mean complex deployments and heavy endpoint agents. Red Access provides a seamless, agentless path to achieving comprehensive Zero Trust architecture. Because the web browser is the primary workspace for modern employees, Red Access secures the enterprise right at this critical juncture.
How Red Access Enables Zero Trust:
- Agentless ZTNA: Red Access delivers secure, granular access to corporate web applications without requiring any software installation on the endpoint. This makes it the perfect solution for securing BYOD and third-party contractors.
- Context-Aware Authentication: Access is evaluated continuously based on user identity, device posture, and behavior, ensuring that only authorized users can reach specific applications.
- Total Session Isolation: By securing the browsing session itself, Red Access prevents malicious code from reaching the device and stops sensitive corporate data from leaking out, effectively neutralizing phishing and ransomware threats.
- Frictionless Deployment: IT teams can roll out Red Access across the organization in minutes, drastically reducing the management overhead associated with traditional security tools.
Transitioning to a Zero Trust framework is a critical step for modern IT infrastructure. With Red Access, businesses can implement granular, secure access controls that protect their assets while empowering a flexible, productive workforce.